Hello Folks,
This blog focuses on the identification and exploitation of HTTP Host header vulnerability. We will understand this vulnerability and then see how we can perform password reset poisoning via middleware. We will be utilizing the PortSwigger platform to understand this vulnerability. So, let’s begin and understand this vulnerability before exploiting it.
The host header is an essential HTTP request header that allows our request to reach the desired domain name. The HTTP Host header vulnerability arises when the server doesn’t validate the value of the Host header and processes it. An attacker can easily identify this vulnerability and can perform server-side attacks like password reset poisoning, web cache poisoning, SQL injection, routing-based SSRF, etc.
Lab- Password reset poisoning via Middleware
Let’s open this lab on PortSwigger and read the lab description. This lab requires Burp Suite community edition.
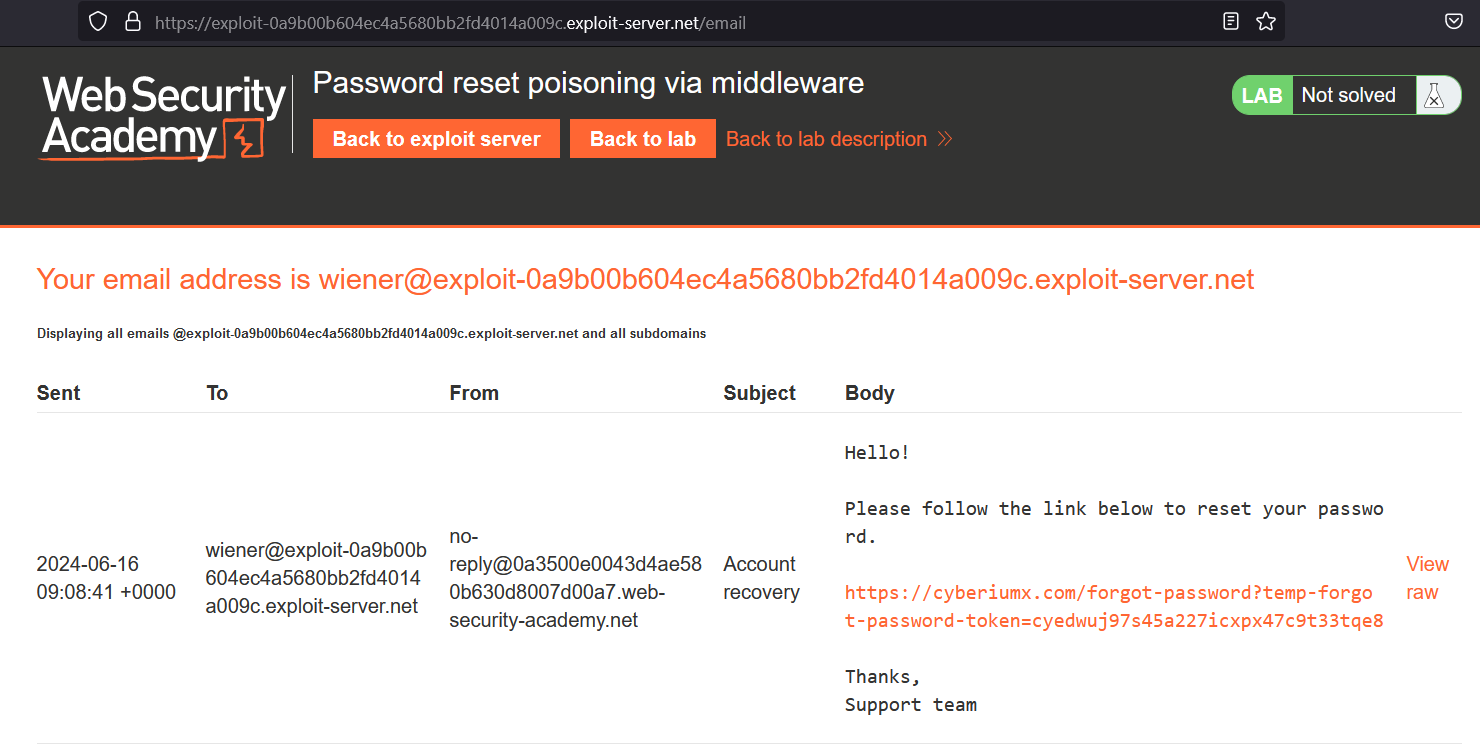
We have to target the password reset functionality which we can find after clicking on the “My account” button. We are asked to provide the username or email address of the user. For now, we will provide Wiener as our username. We will receive a password reset link on our email client which is available on the exploit server. We can click on the link and provide a new password for the wiener user.
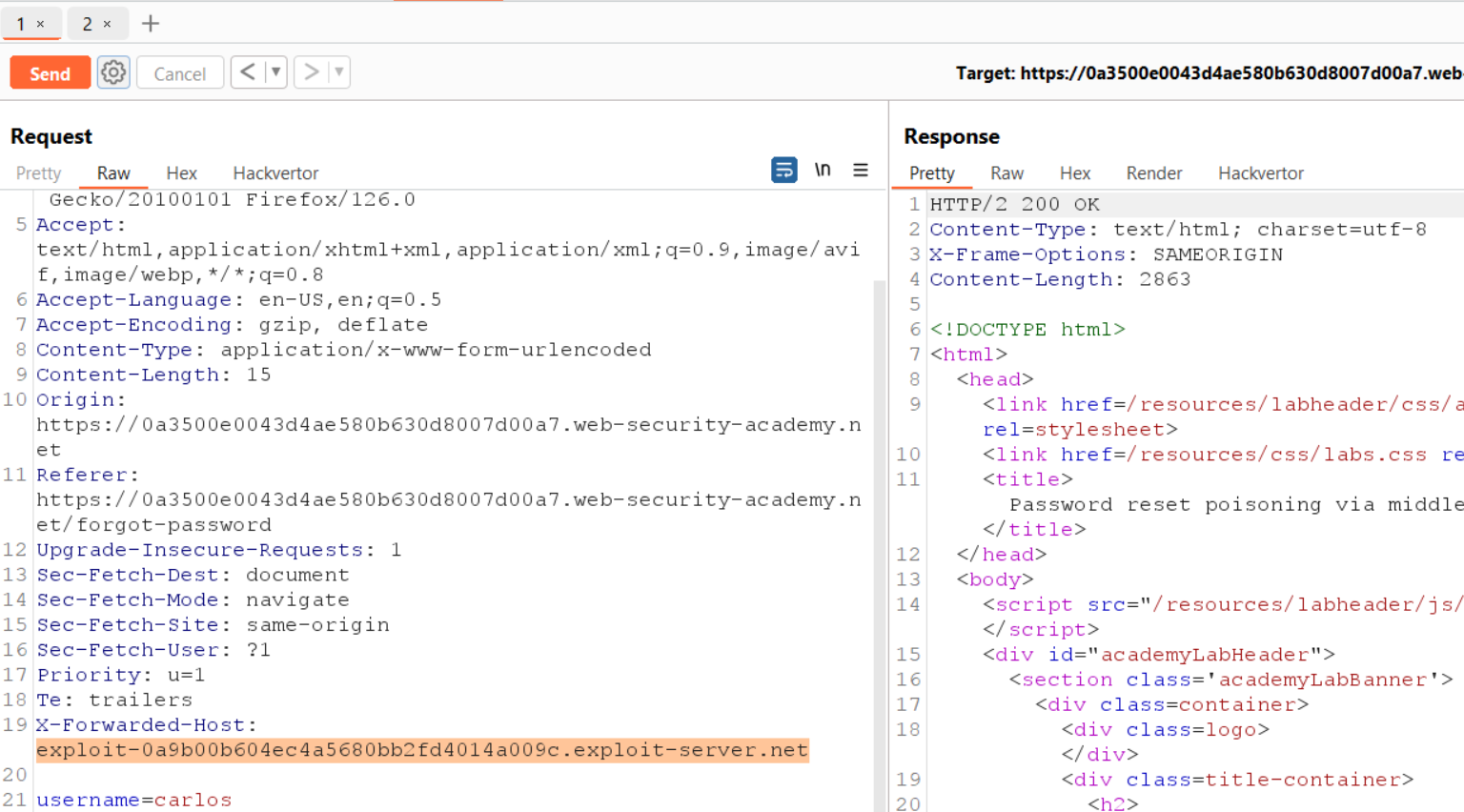
Now after exploring the password reset functionality, we will try to identify the vulnerability using Burp Suite. Let’s find a POST request to /forgot-password endpoint and send the request to Repeater. Let’s try to change the value of the original Host header with an arbitrary value and we will find that it is not accepted. So we have to try another way to identify this vulnerability.
We can add another header “X-Forwarded-Host” which if supported by the application can override the original Host header. Let’s provide our arbitrary domain name (cyberiumx.com) and send the request. On our email client, we will find another password reset link that contains our domain name.
It confirms that this functionality is vulnerable with HTTP Host header vulnerability. Now we have to replace the value of the new header with our exploit server URL. Also, we have to change the username to carlos to target the user. Let’s send the request.
Once the password reset link is clicked by the victim user, we will receive the token value on our exploit server logs which we can access from the exploit server by clicking on the “Access log” button. Now we need to copy the token value and use it to reset the password of carlos user using the following URL:
https://<Lab_URL>/forgot-password?temp-forgot-password-token=<Token_value>
We can change the password of carlos user and provide a new password using which we can log in as our victim user. We will find that we have successfully logged in as carlos and hence the lab is solved.
In this scenario, we saw how we can identify the Host header vulnerability using another request header. In the upcoming labs, we will explore more attacks using HTTP Host header vulnerability.
You can also explore other Web application vulnerabilities on our website.
Happy Pentesting!
Team CyberiumX