7X-Security with CyberiumX
The digital world has transformed how businesses operate. Organizations now rely heavily on websites, cloud systems, digital payments, and social media platforms to communicate with customers and run operations. While this digital transformation creates massive opportunities, it also opens doors for cybercriminals who constantly search for weaknesses in systems. Cybersecurity has therefore become one of the most important priorities for companies across the world.
Recent statistics show how serious the situation has become. In 2025 alone, 12,195 confirmed data breaches were recorded globally, the highest ever reported. Cyberattacks now occur approximately every 39 seconds worldwide, affecting businesses of all sizes. Even more concerning is the financial impact—the average global cost of a data breach is around $4.4 million, which can cripple small and medium businesses.
Experts also estimate that cybercrime could cost the global economy $10.5 trillion annually by 2025, making it one of the largest economic threats in the world today. These numbers highlight a simple truth: cyber threats are not slowing down; they are evolving faster than ever. Attackers are using advanced technologies such as artificial intelligence, automated hacking tools, and sophisticated social engineering tactics to compromise systems.
Businesses today face threats ranging from ransomware attacks and phishing scams to credential theft and cloud misconfigurations. Many organizations believe they are too small to be targeted, but in reality, cybercriminals often prefer smaller companies because they tend to have weaker security measures. This is exactly why companies need a structured and layered cybersecurity strategy that protects every digital asset within their ecosystem.
Why Every Business is a Target Today
Think of cybersecurity like protecting a building. If a building has only one door lock but dozens of windows left open, intruders will simply find another way inside. The same principle applies to cybersecurity. Businesses may install antivirus software or a firewall and assume they are safe, but attackers rarely rely on a single method. Instead, they exploit multiple vulnerabilities simultaneously.
Modern cyber attackers target businesses through several entry points. Websites with coding vulnerabilities can allow hackers to inject malicious scripts or steal sensitive data. Social media accounts can be hijacked through phishing attacks or weak passwords, damaging brand reputation. Corporate networks can be infiltrated through misconfigured routers or insecure remote access systems. Even employees themselves can unknowingly become gateways for cyberattacks by clicking on malicious links or downloading infected files.
Studies show that 68% of security breaches involve human error, demonstrating how attackers often manipulate people rather than just technology. In many cases, cybercriminals do not need advanced hacking skills; they simply trick employees into revealing login credentials or sensitive information.
As businesses expand their digital presence through cloud computing, mobile applications, and third-party integrations, the attack surface continues to grow. A single vulnerability in any system component can compromise the entire organization. This is why relying on a single security solution is no longer enough. Companies must adopt a multi-layer cybersecurity approach, ensuring that even if one defense fails, other layers continue protecting the organization.
Why Businesses Need Multi-Layer Cybersecurity Protection
For many years, organizations relied on traditional security solutions such as antivirus software, firewalls, or intrusion detection systems. While these tools remain important, they are no longer sufficient on their own. Cyber attackers today operate like highly organized businesses with specialized tools, automated attack frameworks, and global networks.
Traditional security approaches usually focus on a single protection point, such as blocking malware or filtering network traffic. Unfortunately, cybercriminals rarely attack through just one channel. They combine multiple techniques to bypass defenses. For example, an attacker might send a phishing email to an employee, steal their login credentials, and then use those credentials to access a company’s cloud infrastructure.
Another limitation of traditional security systems is that they often detect threats only after an attack has already begun. By the time an organization realizes something is wrong, sensitive data may already have been stolen or encrypted by ransomware. This reactive approach makes it difficult for companies to stay ahead of attackers.
Cybersecurity experts therefore recommend adopting defense-in-depth strategies, also known as layered security models. This approach ensures that security measures are applied at multiple levels—including infrastructure, applications, users, networks, and monitoring systems. Even if one layer is bypassed, the next layer continues to protect critical systems.
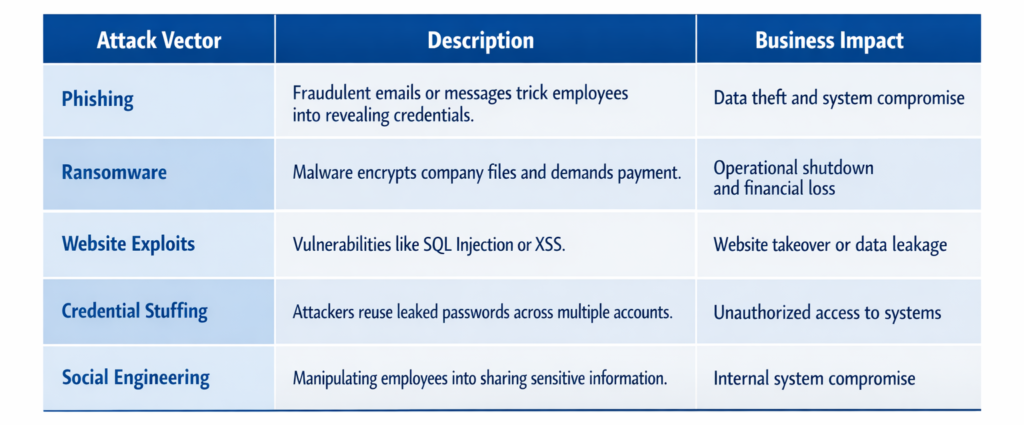
Common Cyber Attack Vectors Targeting Businesses
Modern cyber attacks use a wide range of techniques, many of which exploit weaknesses across different parts of a company’s digital infrastructure. Some of the most common attack vectors include:
These attack vectors demonstrate why cybersecurity cannot rely on just one defense mechanism. Businesses must protect their networks, applications, employees, digital platforms, and monitoring systems simultaneously.
This is where CyberiumX introduces its 7-Layer Cybersecurity Protection Framework, known as 7-x Security by CyberiumX, designed to provide comprehensive protection against modern cyber threats.
Overview of CyberiumX 7X Protection Framework
Layered cybersecurity works much like the security system of a modern airport. Before passengers reach the aircraft, they pass through multiple checkpoints—identity verification, baggage screening, body scanning, and security patrols. Even if one control fails, others continue protecting the system.
The CyberiumX 7-Layer Cybersecurity Protection Model applies the same philosophy to digital security. Instead of focusing on a single protection mechanism, it secures every critical component of an organization’s infrastructure.
The seven layers include:
- Security Auditing
- Penetration Testing
- Website Security Protection
- Social Media Security
- Network Security Assessment
- Employee Security Awareness
- Continuous Security Monitoring
Each layer plays a specific role in protecting businesses against cyber threats.
Key Objectives of CyberiumX Security Model
The primary goal of this framework is not just to react to cyberattacks but to prevent them before they occur. CyberiumX focuses on identifying vulnerabilities early and strengthening defenses proactively.
The framework aims to achieve several objectives:
- Detect hidden vulnerabilities across systems
- Strengthen network and application security
- Protect brand identity across digital platforms
- Educate employees about cyber threats
- Continuously monitor systems for suspicious activity
By implementing these multiple layers of protection, businesses significantly reduce their chances of falling victim to cybercrime.
Layer 1 – Security Auditing
Security auditing serves as the foundation of strong cybersecurity. Before organizations can defend themselves effectively, they must understand their current security posture. A security audit provides a comprehensive evaluation of existing systems, policies, and infrastructure.
CyberiumX conducts detailed security audits that analyze every aspect of an organization’s digital environment. This includes reviewing network configurations, application security, access controls, and compliance policies. The goal is to identify vulnerabilities before attackers discover them.
Key Components of a Security Audit
A comprehensive security audit typically includes several important activities:
- Infrastructure Security Assessment – Evaluating servers, networks, and systems for weaknesses.
- Vulnerability Scanning – Identifying known security flaws in software or configurations.
- Policy Evaluation – Reviewing security policies and procedures.
- Risk Assessment – Determining the potential impact of vulnerabilities.
Through these activities, organizations gain a clear understanding of their security risks and can implement targeted improvements.
Layer 2 – Penetration Testing (Pentesting)
Penetration testing, often referred to as ethical hacking, involves simulating real-world cyberattacks to evaluate the effectiveness of security defenses. CyberiumX security professionals act like attackers, attempting to exploit vulnerabilities within an organization’s systems.
The purpose of penetration testing is not to damage systems but to identify weaknesses before malicious hackers do. CyberiumX offers various types of pentesting services, including network penetration testing, web application testing, API security testing, and cloud security testing.
This proactive approach allows businesses to fix vulnerabilities before they become security incidents.
Layer 3 – Website Security Protection
Websites are among the most common targets for cyber attackers because they are publicly accessible and often connected to sensitive databases. Attackers frequently exploit vulnerabilities such as SQL injection, cross-site scripting (XSS), broken authentication mechanisms, and insecure file uploads.
CyberiumX helps businesses secure their websites by conducting vulnerability assessments and recommending security improvements. The organization also provides guidance on secure coding practices and web application firewall implementation.
Continuous monitoring ensures that websites remain protected against malware infections and emerging threats.
Layer 4 – Social Media Security
Social media platforms have become powerful tools for businesses to engage with customers and promote their brands. Unfortunately, these platforms are also attractive targets for cybercriminals who attempt to hijack accounts or impersonate companies.
CyberiumX provides specialized social media security services that protect brand identity and customer trust. These services include account security audits, brand impersonation monitoring, and secure login configurations.
Protecting social media accounts ensures that attackers cannot misuse company profiles to spread malicious content or scam customers.
Layer 5 – Network Security Assessment
Corporate networks are often targeted by attackers attempting to gain unauthorized access to internal systems. Once inside the network, attackers may move laterally across systems, steal sensitive data, or install malware.
CyberiumX conducts detailed network security assessments to identify weaknesses in routers, switches, firewalls, and internal configurations. These assessments help organizations strengthen their network architecture and implement proper access controls.
Layer 6 – Employee Security Awareness Training
Technology alone cannot protect organizations from cyber threats. Human behavior plays a critical role in cybersecurity. Employees who are unaware of cyber risks may accidentally expose sensitive information or fall victim to phishing attacks.
CyberiumX provides cybersecurity awareness training programs that educate employees about common threats such as phishing, social engineering, and password security.
When employees understand how cyber attacks work, they become the first line of defense against potential threats.
Layer 7 – Continuous Security Monitoring and Support
Cybersecurity is not a one-time task; it is an ongoing process. New vulnerabilities appear daily, and attackers continuously develop new techniques. Continuous monitoring ensures that organizations remain protected even as threats evolve.
CyberiumX provides ongoing security monitoring, vulnerability assessments, incident response support, and threat analysis. This continuous approach allows businesses to detect suspicious activities early and respond quickly.
Benefits of CyberiumX 7X Cybersecurity Protection
Organizations that implement CyberiumX’s security framework gain several advantages. First, they achieve comprehensive protection against multiple attack vectors, reducing the likelihood of successful cyberattacks. Second, businesses improve their compliance with data protection regulations and industry standards.
Another important benefit is increased customer trust. When organizations demonstrate strong cybersecurity practices, clients feel more confident sharing sensitive information and conducting business online.
CyberiumX combines cybersecurity expertise, ethical hacking techniques, and real-world experience to protect organizations from cyber threats. The company focuses on proactive security strategies that identify vulnerabilities before attackers exploit them.
Organizations choose CyberiumX because it provides customized security solutions tailored to specific business needs.
Conclusion
Cyber threats are growing more sophisticated every year. Businesses that rely solely on basic security tools risk becoming easy targets for cybercriminals. A multi-layer cybersecurity strategy is no longer optional—it is essential.
CyberiumX offers a comprehensive 7-Layer Cybersecurity Protection Framework that secures every part of an organization’s digital ecosystem. From security auditing and penetration testing to employee awareness and continuous monitoring, this approach provides businesses with the protection they need to operate confidently in the digital world.
FAQs
1. What is multi-layer cybersecurity protection?
Multi-layer cybersecurity protection involves implementing several security measures across different systems to defend against cyber threats.
2. Why is penetration testing important?
Penetration testing helps organizations identify vulnerabilities before attackers exploit them.
3. How often should businesses perform security audits?
Most cybersecurity experts recommend conducting security audits at least once a year or after major infrastructure changes.
4. Can small businesses benefit from cybersecurity services?
Yes, small businesses are often targeted by cybercriminals and require strong security measures.
5. How does CyberiumX help organizations stay secure?
CyberiumX provides security auditing, penetration testing, website security, social media protection, network security assessments, employee training, and continuous monitoring.